top of page
Blog
Learn about CSNP, Cyber Safety, technical cybersecurity, and careers in security from our members and volunteers. Interested in contributing?


Security-First Compliance for Small Businesses
Author Karen Walsh Purchase the book from Amazon. The year is 2017. A green-haired, tattooed, pierced mom sits in the back of an...
abdelsyfane
Mar 4, 20246 min read


Unmasking QR Code Scams: Protecting Yourself in the Digital Age
Presented by CSNP's Cyber Safety Dept. Introduction In the era of digital connectivity, QR codes have become ubiquitous, offering a...
abdelsyfane
Feb 19, 20243 min read


The SIEM Playbook: Strategies for Preventing Brute Force Cybersecurity Breaches
Author Gabrielle Hempel In the ever-evolving landscape of cybersecurity, brute force attacks remain a persistent threat to organizations...
abdelsyfane
Jan 22, 202410 min read


The Rise of Spoofed Calls and How to Protect Yourself
Author George Reeves Welcome to the digital jungle, where the convenience of modern communication also brings forth its own share of...
abdelsyfane
Jan 15, 20246 min read


Juice Jacking
Author Chris Thomas Juice jacking is an exploit used to compromise a charging station to infiltrate devices that connect to it. Hackers...
abdelsyfane
Nov 13, 20234 min read


Threat Hunting Metrics: The Good, The Bad and The Ugly
Author Kosta Threat hunting is a crucial aspect of information security, but measuring its effectiveness can be challenging. In this...
abdelsyfane
Oct 16, 20235 min read
Elevating Small Business Cybersecurity: Proven Measures to Safeguard Your Team and Customers
In today's rapidly evolving digital landscape, the paramount significance of cybersecurity cannot be overstated, particularly for small...
abdelsyfane
Aug 28, 20234 min read


EDR Telemetry Project: A Comprehensive Comparison
Author Kostas Endpoint Detection and Response (EDR) products have become essential to organizations’ cybersecurity strategies. As a...
abdelsyfane
Jul 10, 20235 min read


How to Use the Ransomware Control Matrix: A Step-by-Step Guide
Author Ed Rojas In the previous blog, The Ransomware Control Matrix: Introducing a New Framework, we provided a history of how and why...
abdelsyfane
Jun 19, 20238 min read


Brace for Impacket!
Detecting a Red Team (and Threat Actor) Favorite Author Micah Babinski Introduction and Objectives In this article we’ll take on the...
abdelsyfane
Jun 5, 202311 min read


The Ransomware Control Matrix: Introducing a New Framework
Author Ed Rojas As cyber attacks continue to threaten organizations of all sizes, my colleague Aria Rahimi and I recognized the need...
abdelsyfane
May 15, 20233 min read


The Evil Twin – The Cost of Free Wi-Fi
Originally published on Medium on July 15, 2022 Author Harriet Kerubo Growing up, I enjoyed watching Cartoon Network, more so, The Cramp...
abdelsyfane
Mar 20, 20233 min read

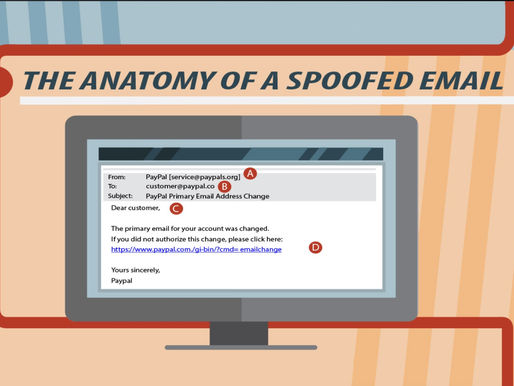
Prevent Email Spoofing with SPF, DKIM and DMARC
Author Fred Luo Email spoofing is one of the common techniques used by phishing attacks. By using different techniques, attackers trick...
abdelsyfane
Feb 27, 20234 min read


Threat Hunting Series: Using Threat Emulation for Threat Hunting
Originally published on October 10, 2022 on Medium. Author Kostas This post will demonstrate how threat emulation can be used for threat...
abdelsyfane
Nov 14, 20227 min read


Video Conferencing & Privacy
Author: Siggi Bjarnason Is Zoom Secure? In today's era of social distancing and bans on large gatherings, it seems everything has gone...
abdelsyfane
Oct 31, 20223 min read


Encryption and the CIA Triad
Photo credit ia.acs.org.au Author: Siggi Bjarnason Introduction Encryption is a type of technology that is embedded in all online...
abdelsyfane
Oct 10, 202212 min read


Threat Hunting Series: The Threat Hunting Process
Originally posted on July 17, 2022 on Medium.com Author: Kostas In the previous posts of the series, I covered the basics of threat...
abdelsyfane
Sep 19, 20228 min read


Understanding Vulnerabilities and a Remediation Walk-Through
Author Ashlyn Matthews In an attempt to practice my blue team skills, I launched a vulnerable instance from AWS and sought out to scan...
abdelsyfane
Sep 12, 20224 min read


Threat Hunting Series: What Makes a Good Threat Hunter
Originally published June 2022 on Medium. Photo by Fahim Reza on Unsplash Continuing with the second post in this series, I felt it was...
abdelsyfane
Aug 15, 20227 min read


Threat Hunting Series: The Basics
Originally posted in June 2022 on Medium Photo by Luke Chesser on Unsplash In recent years, threat hunting has become an important...
abdelsyfane
Aug 8, 20224 min read
bottom of page
